This tech-tip is intended to help resolve card feed problems with Evolis Tattoo2, Evolis Pebble4 and Evolis Dualys3 plastic card printers. Some of the remedies may also apply to other Evolis printers, and those from other manufacturers.

Plastic card printers may have instances when they will not feed cards consistently from their card input hoppers. This can occur when there are just a few cards in the hopper. But it is more common when their card hoppers are full.
Usually, the cause is not with the printer itself. Rather, the problem most often is the result of the cards being difficult to separate.
Card Feed Problems – Remedies:
Before attempting remedies, remember to handle blank plastic cards carefully, and only by their edges. This will prevent the transfer of lint, dust, and residual body-oils from your fingertips. The presence of any of these contaminants can result in poor print-quality.
- Remove the cards from the input hopper and fan out or shuffle them to break any static-bond, and to dissipate natural static charge
- Check the card thickness gauge and set just slightly more than your blank cards’ thickness. For example, if the cards are 30 mils thick, adjust approximately 32 or 33 mils.
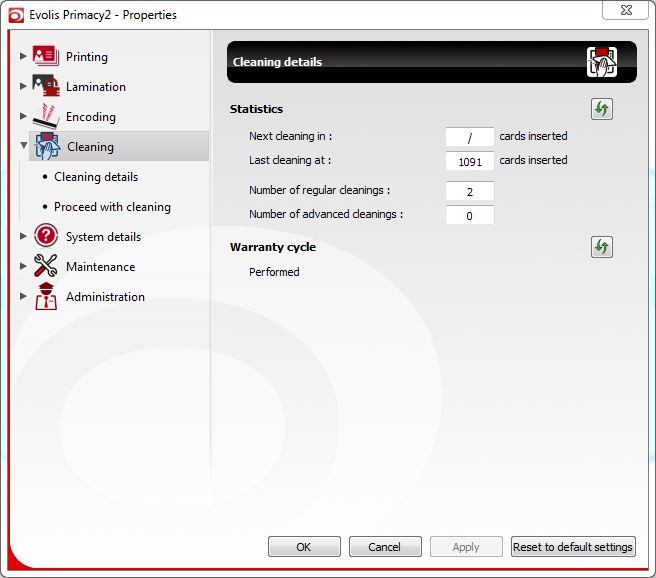
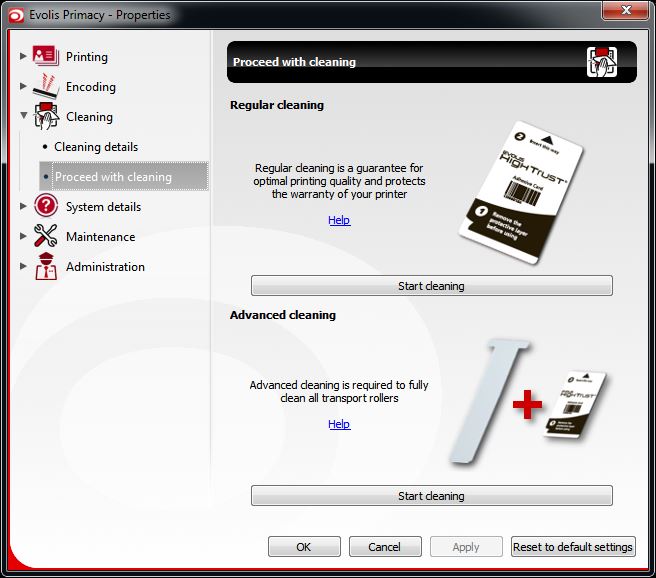
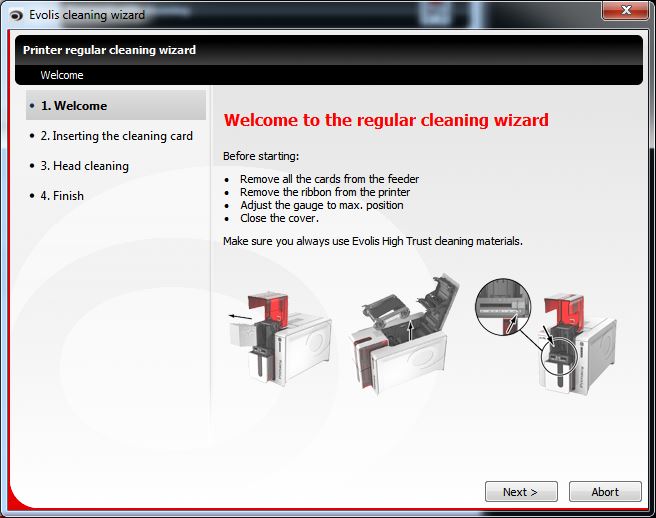
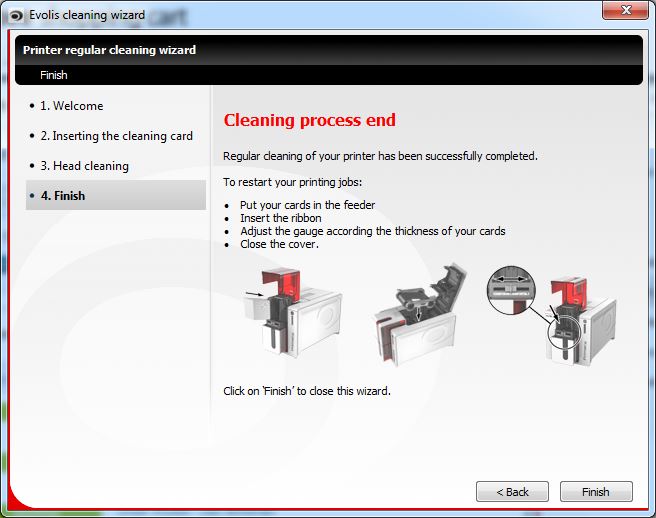
- Clean the card intake roller with alcohol wipes and/or an IPA alcohol cleaning card. Both are included in the Evolis #A5021 UltraClean printer cleaning kit.
- Ensure the cards are stacked properly in the card hopper, and that there are no obstructions that might prevent the printer from extracting them.
Need further assistance or more info?
Safe-Card ID Services offers our clients free telephone-based tech support for the life of all printers sold. For additional assistance, or other information about all Evolis printers, please contact our ID-card experts toll-free at +1 888.485.4696 (US & Canada), or +1 704.535.5200 (elsewhere).
Based in Angers, France, Evolis is a leading global manufacturer of quality plastic card printers.


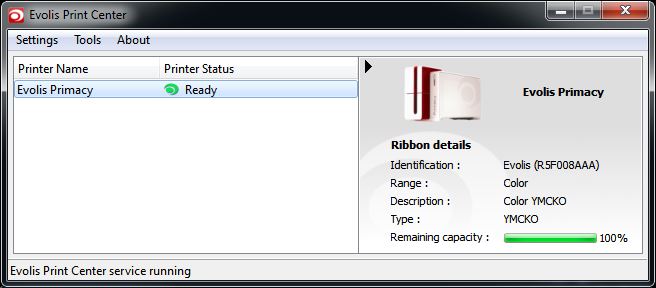
 Evolis has announced that as of December 1, 2016, its Securion printer has entered the End of Life period. The company has made the decision to cease production of this printer following the introduction of a lamination module for its popular Evolis Primacy printer.
Evolis has announced that as of December 1, 2016, its Securion printer has entered the End of Life period. The company has made the decision to cease production of this printer following the introduction of a lamination module for its popular Evolis Primacy printer.